
Dirty COW Vulnerability Advisory
This is a security advisory on the Dirty COW Vulnerability.
What is Dirty COW Vulnerability?
Dirty COW is a privilege escalation vulnerability in the Linux Kernel. The Dirty COW vulnerability allows attackers to gain root access to servers and take control over the whole system and therefore considered as critical vulnerability.
The security hole was detected by researcher Phil Oester, who found out a race condition in the way the Linux kernel’s memory subsystem handles copy-on-write (COW) breakages of private read-only memory mappings. The bug has existed since around 2.6.22 (released in 2007) and was fixed on Oct 18, 2016. Dirty Cow is referenced by CVE-2016-5195.
Dirty Cow is a class of vulnerability known as a “privilege escalation bug”, which means that it allows an attacker which has already gained some measure of control over a specific computer to leverage that into total control.
Who is Vulnerable?
The issue most probably affects number of Linux based machines.
According to the reports, the following Linux distro versions are vulnerable (please note that this is not a complete list but rather a list of the most popular Linux distros):
- Red Hat Enterprise Linux 7.x
- Red Hat Enterprise Linux 6.x
- Red Hat Enterprise Linux 5.x
- CentOS Linux 7.x
- CentOS Linux 6.x
- CentOS Linux 5.x
- Debian Linux wheezy
- Debian Linux jessie
- Debian Linux stretch
- Debian Linux sid
- Ubuntu Linux precise (LTS 12.04)
- Ubuntu Linux trusty
- Ubuntu Linux xenial (LTS 16.04)
- Ubuntu Linux yakkety
- Ubuntu Linux vivid/ubuntu-core
- SUSE Linux Enterprise 11 and 12.
- Openwrt
- Android
How to check if server is vulnerable
Ubuntu/Debian systems.
To find out if your server is affected, check your kernel version.
uname -rv
You’ll see output like this:
Output:
4.4.0-42-generic #62-Ubuntu SMP Fri Oct 7 23:11:45 UTC 2016
If your version is earlier than the following, you are affected:
- 4.8.0-26.28 for Ubuntu 16.10
- 4.4.0-45.66 for Ubuntu 16.04 LTS
- 3.13.0-100.147 for Ubuntu 14.04 LTS
- 3.2.0-113.155 for Ubuntu 12.04 LTS
- 3.16.36-1+deb8u2 for Debian 8
- 3.2.82-1 for Debian 7
- 4.7.8-1 for Debian unstable
CentOS
Some versions of CentOS can use this script provided by RedHat for RHEL to test your server’s vulnerability. To try it, first download the script.
wget https://access.redhat.com/sites/default/files/rh-cve-2016-5195_1.sh
Then run it with bash.
bash rh-cve-2016-5195_1.sh
If you’re vulnerable, you’ll see output like this:
OutputYour kernel is 3.10.0-327.36.1.el7.x86_64 which IS vulnerable.
Red Hat recommends that you update your kernel. Alternatively, you can apply partial mitigation described at https://access.redhat.com/security/vulnerabilities/2706661
How ControlCase CaaS Customers can request a test for Dirty COW Vulnerability?
ControlCase Compliance as a Service (CaaS) customers can request “Dirty COW Vulnerability Scan” by using following steps:
-
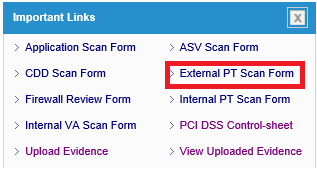
- Login to IT GRC portal
- Click “External PT Scan Form” link on the dashboard
-
- Fill the External Network Penetration Test form with all the details and mention “Dirty COW Vulnerability Scan” before filling public IP addresses against #6

-
- You must provide credentials to do the authenticated scan.
- Once form is filled completely, click Notify button on top right corner.
![]()
Note: We will require credentials (other than root) to detect this flaw during scan.
This scan can also be performed for Internal Systems from the ControlCase Appliance.
How to fix
Ubuntu and Debian
On Ubuntu and Debian, upgrade your packages using apt-get.
sudo apt-get update && sudo apt-get dist-upgrade
You can update all of your packages on CentOS 6 and 7 with sudo yum update, but if you only want to update the kernel to address this bug, run:
sudo yum update kernel
References and Useful Links
https://dirtycow.ninja/
https://github.com/dirtycow/dirtycow.github.io/wiki/VulnerabilityDetails
https://www.siteground.com/blog/dirty-cow-vulnerability/
https://www.digitalocean.com/community/tutorials/how-to-protect-your-server-against-the-dirty-cow-linux-vulnerability